Generate Encryption Key From Password
2023-01-30

When you generate an encryption key from a password using our offline tool, a fixed salt is used. This means that the same password always results in the same key. While this can be convenient, it also increases the risk, as an attacker could precompute a table of possible keys and try to decrypt your data. Because we'll never change the salt or the parameters, they have all the time in the world to calculate that table.
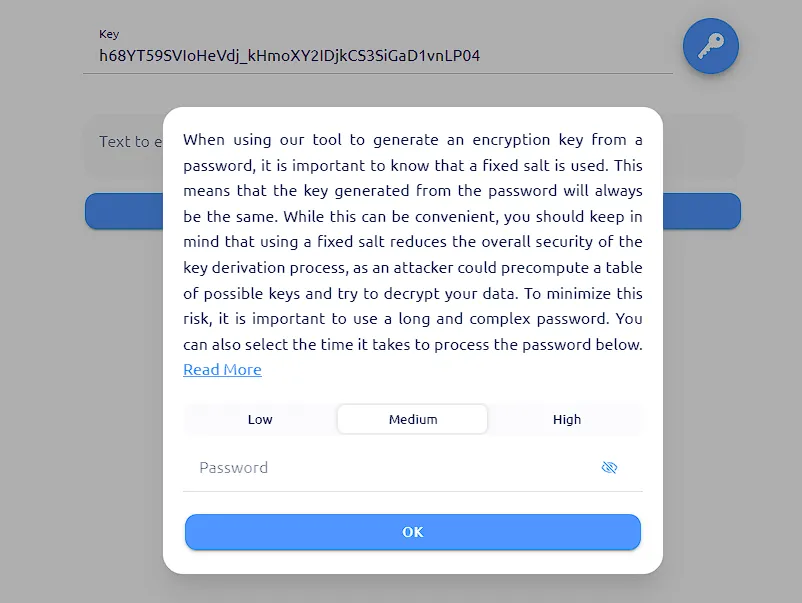
To minimize this risk, it's important to use a long and complex password. However, a complex password alone may not be enough. That's why we have adjustable security levels to reduce the risk of using a fixed salt. We offer you three security levels to generate the password. Each level increases the operations and memory limit for the Argon2id algorithm, making it more time-consuming to process the password. The low level takes only a few seconds on a normal computer, while the high level takes almost a minute. This makes the pre-calculation of the keys more expensive, but by no means impossible.
When it comes to passwords, convenience and security are often in conflict. A password that is easy to remember is also easier to crack, and a password that is hard to crack is often hard to remember. To avoid this, it's recommended to use a random password instead of a commonly used or easy-to-guess password. One popular method for creating a strong password is the "Correct Horse Battery Staple" technique, which involves combining several unrelated words to create a passphrase that is easy to remember yet difficult for an attacker to guess.
Using a random password greatly increases the security of your encrypted data, as it's much more difficult for an attacker to guess the password. Generating a strong, complex password can be a challenge, especially if you have to remember it. We highly recommend using a password manager to securely generate and store random passwords for all your accounts.
Code
We use libsodium crypto_pwhash function with a fixed salt ("ThisIsNotRandom!") to generate the key from the password:
Sodium.crypto_pwhash(
Sodium.crypto_secretstream_xchacha20poly1305_KEYBYTES,
“ThePassword”,
Sodium.from_string('ThisIsNotRandom!'),
OpsLimit,
MemLimit,
Sodium.crypto_pwhash_ALG_ARGON2ID13
);
- Low - OpsLimit = 6, MemLimi = 64000000
- Medium - OpsLimit = 12, MemLimit = 128000000
- High - OpsLimit = 50, MemLimit = 256000000
Example
With this tool and a weak password like "Password123!" you'd get these results:
- Low "-maMhztdjw6wHRbjG2HMOou_anmML0bmmclRqsFBwZ0" (3 seconds)
- Medium "ZVN2SvqL_v1-P4L3xWnec9QpF5Ei4sbswGdq8dtIII4" (10 seconds)
- High "iGp9R9MoICu6oPLfos-amkh767Ed30-vtIwE5m_YV4o" (80 seconds)
If the password you used is in a dictionary, the attacker can easily generate the keys and try them. It's only a matter of time. That is why it's very important to create a password that cannot be guessed, for example, the name of your pet, the year of birth of your children, the name of your company, etc. All of these can be tried, even if it takes more than a minute to generate.
Conclusion
In summary, it's important to understand the risks associated with using this feature and take steps to mitigate this risk by using a long and complex password. We can't stress enough how important it is to use a random password whenever possible, as this will significantly increase the security of your data. Keep in mind that the use of a fixed salt limits the security of this key generation method, and it's crucial to use a random password and a password manager to store it securely.
Although this key generation method may not adhere to all security best practices, it can be useful if used carefully. By implementing the adjustable security levels, utilizing the "Correct Horse Battery Staple" technique for generating strong passwords, and employing a password manager for secure storage, you can improve the security of your encrypted data while still maintaining the convenience of using the same key for the same password.
